
Information system security audit mainly includes data security, operating system security, database system security, network security, equipment security, environmental security, etc. The operating system is between hardware and other software, which is the basis for all software operation, so the security of the operating system determines the security of the entire software system.
Information system security audit also includes the review of external attacks and internal abuses.Auditors will evaluate the system's intrusion detection and defense measures, as well as monitoring and audit measures for employees and administrators to prevent potential security threats and abuses.
The main objects of information security audit are users, hosts and nodes.
The log audit system is used to comprehensively collect logs (including operation, alarm, operation, operation, message, status, etc.) generated by common security equipment, network equipment, database, server, application system, host and other equipment in enterprise IT system, and store, monitor, audit, analyze, Alarm, response and reporting system.
The security audit system generally refers to the security audit system on the computer, which is designed to prevent the leakage of important data in enterprise computers.
Network securityThe components of the whole audit system are as follows: data acquisition The network security audit system first needs to have the ability to collect data, which includes real-time collection and storage of network traffic, system logs, security events and other information.

1. Traditional audit and computer audit, the basic audit objectives and audit scope are the same. The differences between the two are mainly reflected in the changes in audit methods and technologies and the differences in audit risks.
2. The audit content is different. The accounting computerized information system greatly reduces calculation or accounting errors, but the accounting computerized system may be used by fraudulent programs or hackers, and it is not easy to detect, and there are relatively large system security problems. The technical methods are different.
3. Manual audit, that is, traditional audit, called "manual" is for "computer". Usually, what we call computer audit has two meanings: one is to audit the accounting information system; the other is to use computers to audit. Due to the development of accounting computerization and the differences in the tools used by the two, the differences between them have led to them.
4. The difference between data audit and information system audit is reflected in the different angles of data utilization between the two. Data-based audit focuses on the relationship between data and mainly audits the results of data, while information system audit mainly focuses on the authenticity and integrity of data, and audits the security and reliability of the system by testing the authenticity and integrity of data.
5. The object of audit is different: the object of data audit is the electronic data stored and processed in the information system, and the object of the information system audit is the information system that stores and processes electronic data.
The main functions of the security audit system include the automatic response function of security audit, securityFull audit data generation function, security audit analysis function, security audit browsing function, security audit event selection function.
The main functions of the security audit system are as follows: a tool for tracking and comprehensively sorting out the use status of the network or designated system, which is mainly divided into two types: user autonomous protection and system audit protection.
The main functions of security audit are as follows: automatic response function of security audit. Security audit data generation function. Security audit and analysis function. Security audit browsing function. Security audit event selection function. Security audit event storage function.
Binance wikipedia-APP, download it now, new users will receive a novice gift pack.
Information system security audit mainly includes data security, operating system security, database system security, network security, equipment security, environmental security, etc. The operating system is between hardware and other software, which is the basis for all software operation, so the security of the operating system determines the security of the entire software system.
Information system security audit also includes the review of external attacks and internal abuses.Auditors will evaluate the system's intrusion detection and defense measures, as well as monitoring and audit measures for employees and administrators to prevent potential security threats and abuses.
The main objects of information security audit are users, hosts and nodes.
The log audit system is used to comprehensively collect logs (including operation, alarm, operation, operation, message, status, etc.) generated by common security equipment, network equipment, database, server, application system, host and other equipment in enterprise IT system, and store, monitor, audit, analyze, Alarm, response and reporting system.
The security audit system generally refers to the security audit system on the computer, which is designed to prevent the leakage of important data in enterprise computers.
Network securityThe components of the whole audit system are as follows: data acquisition The network security audit system first needs to have the ability to collect data, which includes real-time collection and storage of network traffic, system logs, security events and other information.

1. Traditional audit and computer audit, the basic audit objectives and audit scope are the same. The differences between the two are mainly reflected in the changes in audit methods and technologies and the differences in audit risks.
2. The audit content is different. The accounting computerized information system greatly reduces calculation or accounting errors, but the accounting computerized system may be used by fraudulent programs or hackers, and it is not easy to detect, and there are relatively large system security problems. The technical methods are different.
3. Manual audit, that is, traditional audit, called "manual" is for "computer". Usually, what we call computer audit has two meanings: one is to audit the accounting information system; the other is to use computers to audit. Due to the development of accounting computerization and the differences in the tools used by the two, the differences between them have led to them.
4. The difference between data audit and information system audit is reflected in the different angles of data utilization between the two. Data-based audit focuses on the relationship between data and mainly audits the results of data, while information system audit mainly focuses on the authenticity and integrity of data, and audits the security and reliability of the system by testing the authenticity and integrity of data.
5. The object of audit is different: the object of data audit is the electronic data stored and processed in the information system, and the object of the information system audit is the information system that stores and processes electronic data.
The main functions of the security audit system include the automatic response function of security audit, securityFull audit data generation function, security audit analysis function, security audit browsing function, security audit event selection function.
The main functions of the security audit system are as follows: a tool for tracking and comprehensively sorting out the use status of the network or designated system, which is mainly divided into two types: user autonomous protection and system audit protection.
The main functions of security audit are as follows: automatic response function of security audit. Security audit data generation function. Security audit and analysis function. Security audit browsing function. Security audit event selection function. Security audit event storage function.
OKX Wallet apk download latest version
author: 2025-01-10 11:36 OKX Wallet
OKX Wallet
243.59MB
Check Binance US
Binance US
496.35MB
Check OKX Wallet
OKX Wallet
248.72MB
Check Binance login
Binance login
465.59MB
Check OKX Wallet APK
OKX Wallet APK
115.18MB
Check Binance login App
Binance login App
615.97MB
Check Binance wikipedia
Binance wikipedia
378.84MB
Check OKX Wallet app
OKX Wallet app
165.55MB
Check Binance app
Binance app
929.78MB
Check OKX Wallet download
OKX Wallet download
272.59MB
Check OKX Wallet
OKX Wallet
491.42MB
Check Binance APK
Binance APK
817.37MB
Check OKX Wallet login
OKX Wallet login
361.45MB
Check Binance app
Binance app
381.78MB
Check OKX review
OKX review
497.69MB
Check okx.com login
okx.com login
428.35MB
Check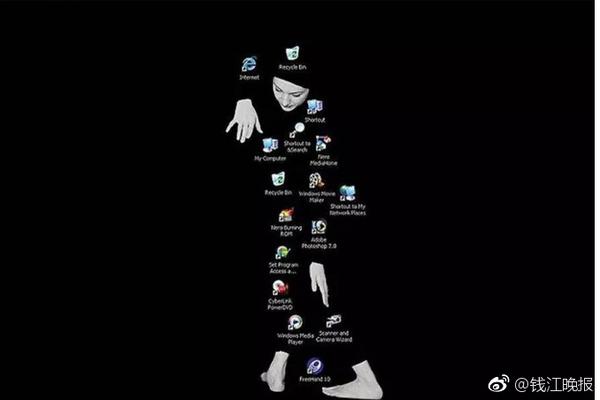 OKX review
OKX review
974.48MB
Check Binance app
Binance app
249.89MB
Check Binance app
Binance app
746.11MB
Check Binance download
Binance download
696.28MB
Check Binance APK
Binance APK
328.68MB
Check OKX Wallet apk download latest version
OKX Wallet apk download latest version
386.66MB
Check Binance download
Binance download
226.24MB
Check OKX review
OKX review
717.17MB
Check Binance APK
Binance APK
394.52MB
Check OKX review
OKX review
832.57MB
Check Binance APK
Binance APK
721.91MB
Check Binance download Android
Binance download Android
465.58MB
Check Binance login App
Binance login App
619.19MB
Check Binance APK
Binance APK
416.73MB
Check Binance login
Binance login
495.71MB
Check Binance APK
Binance APK
674.14MB
Check OKX Wallet APK
OKX Wallet APK
261.61MB
Check OKX download
OKX download
914.83MB
Check OKX app
OKX app
985.17MB
Check okx.com login
okx.com login
515.82MB
Check
Scan to install
Binance wikipedia to discover more
Netizen comments More
1045 察言观色网
2025-01-10 12:57 recommend
2271 一语道破网
2025-01-10 12:37 recommend
2097 丧心病狂网
2025-01-10 12:24 recommend
2353 穷山恶水网
2025-01-10 11:45 recommend
2739 固若金汤网
2025-01-10 11:31 recommend